Finest phia liz leaked is a stark reminder of the vulnerability inherent in our digital age, a digital wildfire that ignites discussions round privateness, ethics, and the lengthy attain of the web. The aftermath of such a leak is not only a headline; it is a cascade of penalties, impacting people on a deeply private stage. The psychological toll will be immense, weaving threads of disgrace, nervousness, and isolation into the material of day by day life.
The ripple impact extends into skilled spheres, probably hindering profession prospects and damaging reputations. We delve into the intricate net of authorized and moral issues that come up, exploring the duties of platforms, the ramifications of non-consensual content material distribution, and the various authorized landscapes throughout the globe. This isn’t nearly a single incident; it is a lens by which we study the broader societal attitudes, cultural responses, and the crucial want for proactive safety in an more and more interconnected world.
This dialogue will meticulously dissect the impression of social media algorithms, and the way they gas the fast unfold of leaked content material. We’ll discover the echo chambers and on-line communities that amplify visibility and dialogue, and the challenges in controlling the unfold of this content material. We’ll discover how societal perceptions are formed by gender, age, and socioeconomic standing, making a framework of how people are handled after their non-public media is leaked.
Moreover, we’ll present actionable methods for safeguarding private data, reporting leaked content material, and constructing a proactive protection towards digital vulnerabilities. This complete evaluation goals to light up the multifaceted dimensions of this delicate concern, providing insights and steerage for navigating the digital panorama.
How does the dissemination of personal media have an effect on a person’s popularity and private life after its public launch?: Finest Phia Liz Leaked

The unauthorized distribution of personal media, whether or not photographs, movies, or different private content material, can have devastating and far-reaching penalties. This breach of privateness not solely violates a person’s rights but in addition exposes them to a variety of potential harms, impacting their popularity, private relationships, psychological well being, {and professional} prospects. The ripple results of such leaks will be felt for years, leaving lasting scars on the sufferer’s life.
Potential Lengthy-Time period Psychological Impacts
The expertise of getting non-public media leaked publicly can set off a cascade of adverse psychological results. The preliminary shock and disbelief usually give technique to a chronic interval of emotional misery.
- Disgrace and Humiliation: The publicity of intimate particulars can result in intense emotions of disgrace and humiliation. Victims could really feel uncovered, weak, and judged by others. This disgrace will be compounded by societal stigmas surrounding the content material of the leaked media, resulting in self-blame and a diminished sense of self-worth.
- Anxiousness and Worry: The fixed worry of judgment, the anticipation of additional publicity, and the uncertainty concerning the future can gas persistent nervousness. Victims could expertise panic assaults, sleep disturbances, and a pervasive sense of unease. They may turn out to be hyper-vigilant, continually monitoring their on-line presence and fearing social interactions.
- Social Isolation and Withdrawal: Leaked media can injury relationships and erode belief. Victims could withdraw from social actions to keep away from scrutiny or judgment. Pals, members of the family, and even companions may distance themselves, resulting in profound emotions of loneliness and isolation. The worry of being perceived negatively can forestall victims from looking for assist and sustaining wholesome relationships.
- Despair and Suicidal Ideation: The mix of disgrace, nervousness, social isolation, and reputational injury can considerably enhance the danger of melancholy. In extreme circumstances, victims could expertise suicidal ideas or try suicide. The emotional toll of a media leak will be overwhelming, {and professional} psychological well being assist is essential for restoration.
- Submit-Traumatic Stress Dysfunction (PTSD): For some people, the expertise of a media leak will be so traumatic that it triggers signs of PTSD. These signs can embody flashbacks, nightmares, hyper-vigilance, and avoidance behaviors. The fixed reminder of the violation could make it tough to perform usually and may considerably impair their high quality of life.
Difficulties in Skilled Settings and Employment Alternatives
The repercussions of a media leak usually prolong past the non-public sphere, considerably impacting a person’s skilled life. Employers, colleagues, and potential purchasers could view the leaked content material unfavorably, resulting in reputational injury and profession setbacks.
- Job Loss and Problem Discovering Employment: Employers could also be hesitant to rent or retain people whose non-public media has been leaked, fearing reputational injury to their firm. A leaked picture or video, no matter its context, can be utilized to make adverse judgments about an individual’s character and professionalism. This will result in job loss or make it extraordinarily tough to safe new employment alternatives.
- Injury to Skilled Popularity: Even when a person retains their job, a media leak can severely injury their skilled popularity. Colleagues and purchasers could lose belief in them, resulting in strained relationships and diminished alternatives for development. The person may be excluded from tasks, missed for promotions, and even subjected to harassment within the office.
- Influence on Future Profession Prospects: The web’s permanence implies that leaked media can resurface years later, probably impacting future profession prospects. Background checks, on-line searches, and social media scrutiny can reveal the leaked content material, making it tough to beat the adverse perceptions related to it. This will restrict profession selections and alternatives for skilled development.
- Lack of Enterprise Alternatives: For entrepreneurs, freelancers, or these in client-facing roles, a media leak can result in the lack of enterprise alternatives. Shoppers could also be hesitant to work with people whose private lives have been uncovered, fearing that their affiliation with them may injury their very own popularity. This will result in a big lack of revenue and a setback of their enterprise endeavors.
- Examples of Actual-World Penalties:
- In 2014, a number of celebrities had non-public pictures leaked, leading to important public scrutiny and, in some circumstances, profession setbacks. The leaks sparked widespread debate about privateness, consent, and the duty of the media.
- A 2017 examine discovered that people with adverse on-line reputations confronted important challenges in securing employment, notably in fields the place popularity is crucial, similar to finance and public relations.
- The case of a instructor whose non-public pictures had been leaked on-line led to her dismissal from her job and a chronic authorized battle to clear her title. This case highlights the devastating impression that such leaks can have on a person’s skilled life.
Methods for Managing On-line Harassment and Defending Private Privateness
Within the aftermath of a media leak, people should take proactive steps to handle on-line harassment and shield their privateness. This entails a mix of authorized motion, digital footprint administration, and looking for assist from trusted sources.
- Authorized Recourse: Victims ought to contemplate pursuing authorized motion towards these answerable for leaking the media. This will contain submitting a lawsuit for defamation, invasion of privateness, or copyright infringement. Authorized motion may help to carry the perpetrators accountable, search monetary compensation for damages, and acquire courtroom orders to take away the content material from on-line platforms.
- Digital Footprint Administration: It’s essential to take steps to handle and management the web presence. This entails:
- Content material Removing Requests: Contacting web site directors and social media platforms to request the removing of the leaked content material. Whereas removing will be difficult, persistence and authorized threats will be efficient.
- Search Engine Optimization (): Implementing methods to push down adverse search outcomes and promote constructive content material concerning the particular person. This will contain creating new web sites, social media profiles, and fascinating in on-line actions that showcase their constructive attributes.
- Monitoring On-line Mentions: Repeatedly monitoring on-line mentions and responding to adverse feedback or false data. This may help to regulate the narrative and tackle any misinformation which will come up.
- Reporting Harassment and Abuse: Victims ought to report any situations of on-line harassment or abuse to the related platforms and regulation enforcement businesses. This may help to carry the perpetrators accountable and stop additional hurt. It is usually essential to doc all situations of harassment and abuse as proof for authorized motion.
- Looking for Help: Victims ought to search assist from trusted associates, members of the family, or psychological well being professionals. Speaking concerning the expertise and processing the emotional impression is essential for restoration. Help teams and on-line communities may present a way of group and understanding.
- Defending Future Privateness: Taking steps to guard private privateness sooner or later is crucial. This consists of:
- Reviewing Privateness Settings: Repeatedly reviewing and updating privateness settings on social media platforms and different on-line accounts.
- Being Cautious about Sharing Private Data: Being cautious about sharing private data on-line, together with pictures, movies, and placement knowledge.
- Utilizing Sturdy Passwords and Two-Issue Authentication: Utilizing robust passwords and enabling two-factor authentication on all on-line accounts to forestall unauthorized entry.
What authorized and moral issues come up from the unauthorized distribution of intimate content material on the web?
The unauthorized distribution of intimate content material on the web presents a posh net of authorized and moral challenges. This act, also known as “revenge porn” or non-consensual pornography, inflicts important hurt on people and necessitates a radical examination of its ramifications. The fast dissemination capabilities of the web exacerbate the injury, making it essential to know the authorized penalties, moral obligations of platforms, and worldwide authorized variations.
Authorized Ramifications of Distributing Non-Consensual Intimate Pictures
The unauthorized distribution of intimate photographs carries extreme authorized penalties, encompassing each prison fees and civil lawsuits. The precise legal guidelines and penalties range relying on the jurisdiction, however the core precept stays constant: defending people from the exploitation and abuse of their non-public data.The prison fees sometimes contain offenses associated to privateness violations, harassment, and generally, even sexual assault, relying on the context and content material of the photographs.
Prosecutors usually convey fees beneath legal guidelines particularly addressing non-consensual pornography or revenge porn. For instance, in lots of U.S. states, the distribution of intimate photographs with out consent is a felony, carrying potential jail sentences and substantial fines. The severity of the punishment usually is dependent upon components such because the intent of the distributor, the quantity of people that seen the content material, and whether or not the sufferer suffered any threats or harassment in consequence.The authorized frameworks contemplate the distribution itself as against the law, no matter whether or not the photographs had been initially created with consent.
Even when the photographs had been initially taken consensually, their subsequent distribution with out the topic’s permission constitutes a violation.
In California, as an example, Penal Code Part 647(j)(4) makes it a misdemeanor to distribute intimate photographs with out consent, with potential jail time and fines.
Past the direct distribution, people concerned in facilitating the unfold of such content material, similar to those that create web sites or social media accounts particularly for this function, may face prison fees. These fees can embody aiding and abetting or conspiracy. The prosecution should show past an affordable doubt that the defendant knew the content material was non-consensual and acted with the intent to hurt the sufferer.
This usually requires gathering proof from the digital footprint, together with communications, web site logs, and consumer exercise.Civil lawsuits present one other avenue for victims to hunt justice. These lawsuits permit victims to sue the distributors for damages, together with emotional misery, reputational hurt, and monetary losses. The authorized foundation for these lawsuits sometimes entails claims of invasion of privateness, intentional infliction of emotional misery, and defamation.
The sufferer can search financial compensation to cowl the prices of remedy, authorized charges, and different bills related to the hurt attributable to the distribution.The success of a civil lawsuit usually hinges on the power to show that the defendant distributed the photographs with the intent to trigger hurt or acted with reckless disregard for the sufferer’s privateness.
Within the case of Jane Doe v. John Smith, a sufferer efficiently sued her ex-partner for distributing intimate photographs on-line, leading to a considerable monetary settlement to compensate for the emotional misery and reputational injury she suffered.
The authorized course of will be prolonged and sophisticated, requiring the sufferer to assemble proof, rent authorized illustration, and navigate the courtroom system. Nevertheless, a profitable lawsuit can present a measure of justice and compensation for the hurt inflicted.The digital nature of the web presents distinctive challenges to implementing these legal guidelines. The anonymity supplied by some platforms and the worldwide attain of the web make it tough to establish and prosecute offenders.
Worldwide cooperation is usually required to trace down people who distribute content material from completely different international locations. Furthermore, the fixed evolution of know-how and the emergence of recent platforms require authorized frameworks to adapt to remain related and efficient in combating the unfold of non-consensual intimate photographs.
Moral Tasks of On-line Platforms
On-line platforms have a big moral duty to handle and take away leaked content material, balancing free speech with consumer privateness. The dimensions of this duty is appreciable, given the platforms’ roles as conduits for data and their potential to inflict and perpetuate hurt.Platforms should set up clear insurance policies prohibiting the distribution of non-consensual intimate photographs, together with specific definitions of what constitutes such content material.
These insurance policies ought to be readily accessible and simply understood by customers.
Fb, for instance, has a particular coverage towards revenge porn, permitting customers to report situations of non-consensual intimate photographs.
The immediate removing of reported content material is crucial. Platforms ought to implement environment friendly reporting mechanisms, enabling customers to flag inappropriate content material shortly and simply. They have to even have a devoted crew or course of to overview reviews and take applicable motion. This course of ought to ideally embody a verification step to verify the non-consensual nature of the photographs and stop false reviews.The implementation of proactive measures to forestall the unfold of such content material can be essential.
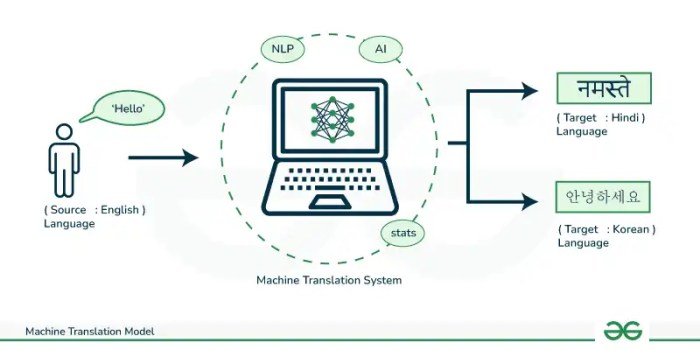
This will embody utilizing synthetic intelligence (AI) and machine studying to establish and take away probably dangerous content material earlier than it’s even reported. These applied sciences can analyze photographs and movies for nudity, sexual content material, and different indicators of non-consensual materials.Transparency and accountability are very important. Platforms ought to be clear about their insurance policies and procedures for dealing with reviews of non-consensual content material. They need to even be accountable for his or her actions, offering updates on the standing of reported content material and the actions taken.Balancing free speech with consumer privateness requires cautious consideration.
Platforms should respect customers’ rights to precise themselves freely whereas additionally defending people from hurt. This entails establishing clear boundaries and balancing these competing pursuits.The safety of consumer knowledge and privateness can be paramount. Platforms ought to take steps to safe consumer knowledge and stop it from being accessed or shared with out consent. This consists of implementing robust safety measures and complying with knowledge privateness rules.The moral duties of on-line platforms prolong past merely eradicating content material.
Platforms may play a task in educating customers concerning the harms of non-consensual content material and offering sources for victims. This will embody partnering with organizations that present assist and counseling to victims.
Worldwide Legal guidelines and Laws
Worldwide legal guidelines and rules relating to the distribution of personal media range throughout jurisdictions, creating a posh and fragmented authorized panorama. The shortage of a universally accepted definition of non-consensual pornography and the differing approaches to freedom of expression additional complicate issues.The authorized frameworks addressing the difficulty vary from complete laws to the absence of particular legal guidelines. Some international locations have enacted particular legal guidelines that criminalize the distribution of intimate photographs with out consent, whereas others depend on current legal guidelines associated to privateness, harassment, or defamation.
Whereas the main points surrounding the “finest phia liz leaked” scenario stay a scorching matter, it is a stark distinction to the potential future issues of automotive know-how. Contemplating developments, the implications of “oil leaking inside automobile 2026” are important, probably resulting in pricey repairs and even security hazards; oil leaking inside car 2026 , is a severe matter. In the end, each eventualities spotlight the significance of staying knowledgeable and ready, whether or not it is navigating the complexities of leaked data or anticipating technological challenges.
In the UK, the “Revenge Pornography” regulation, launched in 2015, makes it a prison offense to share non-public sexual photographs with out consent, carrying a possible jail sentence.
Whereas the web buzzes with the newest on finest phia liz leaked, it is value contemplating the real-world prices of coping with issues, such because the potential injury from a leak. Ignoring points can result in costly repairs, much like the sudden payments that come up when you want to perceive the oil leak price to fix. In the end, similar to addressing these issues promptly, understanding the implications of any leaked data is essential.
America has a patchwork of legal guidelines on the state stage, with some states having complete legal guidelines towards non-consensual pornography, whereas others have extra restricted rules.The enforcement of those legal guidelines additionally varies. Some international locations have devoted regulation enforcement items or businesses to research and prosecute circumstances of non-consensual pornography, whereas others could lack the sources or experience to successfully tackle the difficulty.Worldwide cooperation is essential for combating the worldwide unfold of non-consensual content material.
This consists of cooperation between regulation enforcement businesses, the sharing of knowledge, and the extradition of offenders. Nevertheless, the authorized and cultural variations between international locations could make this cooperation difficult.The position of worldwide organizations in addressing this concern can be important. Organizations such because the United Nations and the Council of Europe have issued suggestions and pointers on combating non-consensual pornography.The evolution of know-how presents a relentless problem to authorized frameworks.
The fast growth of recent platforms and applied sciences requires authorized frameworks to adapt to remain related and efficient.The various approaches to freedom of expression throughout completely different jurisdictions additionally impression the authorized panorama. Some international locations place a higher emphasis on freedom of speech than others, which might affect how they regulate the distribution of intimate content material.The impression of cultural norms and societal attitudes on the authorized panorama shouldn’t be missed.
In some cultures, there could also be a higher stigma related to non-consensual pornography, resulting in stricter legal guidelines and higher social stress to fight the difficulty.
What position does social media play within the unfold and perpetuation of leaked non-public media, and what are its penalties?
Social media platforms have turn out to be the first conduits for the fast and widespread dissemination of leaked non-public media. Their structure, constructed on prompt sharing and world attain, has inadvertently amplified the potential for private data to be uncovered to huge audiences, resulting in extreme repercussions for these affected. The inherent nature of those platforms, coupled with the habits of their customers, creates an ideal storm for the fast propagation and enduring presence of delicate content material.
Social Media Algorithms and Content material Dissemination
Social media algorithms are designed to maximise consumer engagement, usually prioritizing content material that generates excessive ranges of interplay, similar to shares, likes, and feedback. This algorithmic bias inadvertently fuels the unfold of leaked non-public media. The extra engagement a chunk of leaked content material receives, the extra probably it’s to be amplified and proven to a wider viewers, no matter its delicate nature or the hurt it might trigger.
This creates a vicious cycle the place the content material’s visibility will increase exponentially.As an example, contemplate a state of affairs the place a personal video is leaked. The algorithm, detecting a surge in shares and feedback, would probably promote the video to extra customers, even when these customers have not explicitly expressed curiosity in that kind of content material. The platform’s advice methods, designed to recommend comparable content material, would then additional contribute to the unfold.
The thrill round “finest phia liz leaked” continues to flow into, prompting curiosity about the place such content material may floor. Many customers at the moment are looking for out various platforms, main them to discover sources that provide insights into discovering content material, together with details about onlyfans leaked sites 2026. Whereas the seek for particular content material stays energetic, the unique matter of “finest phia liz leaked” stays a big focal point.
Customers who have interaction with the leaked video may be proven different associated content material, or content material from the identical people, perpetuating the publicity.Furthermore, the algorithms’ deal with tendencies and virality usually prioritizes pace over accuracy or moral issues. Content material that beneficial properties traction shortly is usually amplified earlier than moderators can intervene, making it extraordinarily tough to include the unfold as soon as it begins.
That is notably difficult given the sheer quantity of content material uploaded to social media platforms day by day. The pace at which leaked content material can unfold, pushed by algorithmic amplification, usually surpasses the capability of moderation groups to successfully take away it.One particular instance of this may be seen within the dealing with of revenge porn. As soon as shared, the content material usually spreads by a number of platforms and even encrypted messaging apps.
The preliminary platform could take it down, however the content material has already been copied, shared, and re-uploaded elsewhere. This creates a recreation of “whack-a-mole,” the place eradicating the content material on one platform would not forestall its continued existence on others. The algorithm’s inherent traits contribute to this difficult surroundings, making it almost unimaginable to utterly eradicate the leaked content material from the digital panorama.
Influence of On-line Communities and Echo Chambers, Finest phia liz leaked
On-line communities and echo chambers considerably amplify the visibility and dialogue of leaked media, contributing to the extended publicity and potential for additional hurt. These areas, usually constructed round shared pursuits or ideologies, create environments the place leaked content material can flow into freely and be mentioned with restricted crucial scrutiny. The algorithms that govern social media usually contribute to the formation of echo chambers by recommending content material and connections based mostly on customers’ current pursuits and on-line behaviors.Inside these communities, the leaked media will be re-shared, analyzed, and commented on, usually with little regard for the privateness or emotional well-being of the people concerned.
The anonymity afforded by some on-line platforms can additional embolden customers to take part within the unfold and dialogue of the content material, making it tough to carry people accountable for his or her actions.A outstanding instance of this phenomenon will be seen within the aftermath of celeb leaks. Devoted on-line boards and social media teams usually spring up, the place customers dissect the leaked content material, speculate concerning the people concerned, and share unverified data.
These teams, usually comprised of followers or people with particular pursuits, can create a concentrated surroundings for the content material to persist and evolve. The fixed publicity inside these areas can exacerbate the hurt attributable to the preliminary leak, prolonging the trauma and probably resulting in harassment or different types of abuse.The echo chamber impact additionally implies that dissenting voices or makes an attempt to guard the privateness of these concerned are sometimes drowned out or ignored.
The algorithms that drive these communities favor content material that aligns with the group’s prevailing views, additional reinforcing the echo chamber and making it tough for various views to realize traction. This will result in a scenario the place the leaked content material turns into normalized and even celebrated, intensifying the adverse impression on the people affected.
Methods for Mitigating the Unfold of Leaked Content material
Social media platforms can implement a number of methods to mitigate the unfold of leaked content material and reduce its dangerous results. These methods require a multifaceted strategy that mixes technological options, consumer schooling, and proactive monitoring.
- Content material Moderation: Implement sturdy content material moderation insurance policies that explicitly prohibit the sharing of non-consensual intimate photographs or movies. Make use of each automated methods and human moderators to establish and take away leaked content material promptly.
- Consumer Reporting Mechanisms: Present simply accessible and user-friendly reporting mechanisms that permit customers to flag probably dangerous content material. Guarantee a fast response time to reported content material and supply clear suggestions to the reporting consumer.
- Proactive Monitoring: Develop proactive monitoring methods that scan for leaked content material utilizing picture and video recognition know-how, and text-based evaluation. Accomplice with third-party organizations to establish and take away content material that violates platform insurance policies.
- Account Suspension and Enforcement: Implement a transparent coverage relating to account suspension for customers who share or promote leaked content material. Implement these insurance policies constantly and transparently.
- Search Blocking: Work with engines like google to dam search outcomes that hyperlink to leaked content material, making it tougher for customers to seek out the content material on-line.
- Consumer Schooling: Educate customers concerning the dangers of sharing intimate content material and the significance of respecting privateness. Promote media literacy to assist customers critically consider on-line content material and establish potential scams or dangerous actions.
- Collaboration with Legislation Enforcement: Set up clear channels for collaboration with regulation enforcement businesses to report and examine circumstances of leaked content material and maintain perpetrators accountable.
- Information Encryption and Privateness Controls: Implement end-to-end encryption for personal messages and supply customers with sturdy privateness controls to handle their on-line presence.
- Algorithm Changes: Modify algorithms to prioritize consumer security over engagement. Cut back the amplification of content material that’s flagged as probably dangerous or that has been reported by a number of customers.
What are the societal attitudes and cultural responses surrounding the unauthorized launch of personal media, and the way do they differ?
The unauthorized launch of personal media sparks a posh interaction of societal attitudes and cultural responses, various considerably throughout geographical boundaries, generational divides, and socioeconomic strata. These responses vary from condemnation and empathy to voyeurism and victim-blaming, highlighting the multifaceted nature of privateness, consent, and digital ethics within the twenty first century. Understanding these numerous reactions is essential for addressing the hurt attributable to such leaks and fostering a extra accountable on-line surroundings.
Cultural Views on Privateness and Sharing of Intimate Content material
Cultural views on privateness and the sharing of intimate content material are deeply rooted in historic, non secular, and societal norms. These various viewpoints form how people and communities react to the unauthorized dissemination of personal media.In lots of Western cultures, there is a robust emphasis on particular person privateness, notably relating to intimate content material. This attitude usually stems from the Enlightenment values of particular person autonomy and the precise to regulate one’s private data.
Leaks in these societies are sometimes met with widespread condemnation, with authorized and social repercussions for these concerned within the distribution. Nevertheless, the prevalence of social media and on-line sharing has created a rigidity between this very best of privateness and the truth of public publicity.Conversely, some cultures, notably in East Asia, could place a higher emphasis on collective concord and social popularity.
Whereas privateness is valued, the potential for disgrace and lack of face related to leaked intimate content material will be considerably extra damaging. The main focus may shift from the perpetrator to the sufferer, with social ostracization or stress to adapt to societal expectations turning into extra prevalent. That is mirrored within the stricter censorship of such content material in lots of of those areas and the emphasis on defending household honor.In some Latin American cultures, a extra relaxed angle towards private privateness may exist, notably within the context of close-knit communities.
Whereas unauthorized leaks are nonetheless condemned, the response may be extra nuanced, influenced by components similar to social relationships and private connections. The idea of “machismo” or “marianismo” may also affect reactions, with gendered expectations shaping the notion of the people concerned.In distinction, some African cultures possess various views. Conventional African societies could place a powerful emphasis on group and the significance of household, and leaks could lead to shaming and ostracization.These variations spotlight the significance of understanding the cultural context when analyzing the impression of personal media leaks.
Influence of Gender, Age, and Socioeconomic Standing
Gender, age, and socioeconomic standing considerably have an effect on how people are perceived and handled after their non-public media is leaked. These components intersect to create distinctive experiences and vulnerabilities.Girls are sometimes disproportionately focused by the unauthorized launch of intimate content material, going through heightened scrutiny, slut-shaming, and threats of violence. The historic objectification of girls and the prevalence of misogynistic attitudes on-line contribute to this vulnerability.
As an example, the case of a feminine celeb whose non-public pictures had been leaked on-line led to a barrage of hateful feedback and the widespread circulation of the photographs, inflicting important emotional misery and reputational injury.Youthful people, notably youngsters and younger adults, are additionally extremely weak. Their relative lack of expertise with digital media and social media dynamics, coupled with their often-developing sense of id, makes them vulnerable to exploitation and on-line harassment.
The “cyberbullying” phenomenon, the place leaked content material is used to focus on and humiliate people, is especially prevalent amongst this age group. A highschool pupil whose non-public video was shared amongst classmates confronted relentless bullying and social isolation.Socioeconomic standing can exacerbate these vulnerabilities. People from marginalized communities could lack the sources to hunt authorized recourse or entry psychological well being assist after a leak.
Moreover, they may face further discrimination based mostly on their race, ethnicity, or sexual orientation. A low-income particular person, missing the monetary means to rent a lawyer, may battle to take away leaked content material from the web, resulting in continued publicity and harassment.
Frequent Misconceptions and Stereotypes
The unauthorized launch of personal media usually results in the perpetuation of dangerous misconceptions and stereotypes concerning the people concerned. These stereotypes can have devastating penalties for his or her private lives and reputations.
| False impression | Stereotype | Influence |
|---|---|---|
| The person consented to the sharing of the content material. | “They had been asking for it.” | Sufferer-blaming, minimization of the hurt attributable to the leak, and reluctance to supply assist. |
| The person is promiscuous or immoral. | “They’re a slut/participant.” | Social ostracization, injury to skilled alternatives, and erosion of private relationships. |
| The person is looking for consideration or publicity. | “They did it for fame.” | Dismissal of the person’s misery, justification of on-line harassment, and the creation of a hostile on-line surroundings. |
| The person is weak or deserves to be shamed. | “They’re pathetic/deserving of ridicule.” | Elevated psychological well being points, social isolation, and the perpetuation of adverse stereotypes about victims of on-line harassment. |
How can people shield themselves from the potential dangers related to the unauthorized launch of personal media?
The specter of non-public media leaks looms giant within the digital age, demanding proactive measures for self-protection. This isn’t nearly avoiding embarrassment; it is about safeguarding private autonomy, popularity, and psychological well-being. Understanding the dangers is step one, however taking concrete actions is paramount. This information supplies actionable steps and preventative measures to fortify your digital defenses.
Safeguarding Private Data and Stopping Unauthorized Entry
Defending oneself begins with securing all digital accounts and gadgets. This entails a multi-layered strategy, recognizing that no single measure gives full safety, however the cumulative impact considerably reduces vulnerability.
- Strengthen Passwords: Use robust, distinctive passwords for each on-line account. A powerful password consists of a mixture of uppercase and lowercase letters, numbers, and symbols, and is at the very least 12 characters lengthy.
Think about using a password supervisor to generate and retailer these complicated passwords securely.
Don’t reuse passwords throughout completely different platforms; if one account is compromised, all accounts utilizing the identical password are in danger.
- Allow Two-Issue Authentication (2FA): Activate 2FA on all accounts that provide it. This provides an additional layer of safety by requiring a second verification methodology, similar to a code despatched to your cellphone, even when your password is stolen. That is essential for e mail, social media, and banking accounts.
- Safe Gadgets: Repeatedly replace the working methods and software program on all of your gadgets (telephones, computer systems, tablets). Updates usually embody safety patches that repair vulnerabilities. Allow machine encryption to guard knowledge even when the machine is misplaced or stolen. Use robust machine passcodes or biometric authentication.
- Management Social Media Privateness Settings: Assessment and regulate privateness settings on all social media platforms. Restrict who can see your posts, pictures, and movies. Be cautious about accepting buddy requests from individuals you do not know, as they might be potential sources of malicious assaults or scams. Contemplate setting your profiles to personal.
- Be Cautious of Phishing and Scams: Be vigilant about phishing makes an attempt, which contain misleading emails, messages, or web sites designed to steal your private data. By no means click on on suspicious hyperlinks or present delicate data in response to unsolicited requests. All the time confirm the sender’s id earlier than sharing any private knowledge.
- Safe Cloud Storage: Select respected cloud storage suppliers and allow encryption. Assessment the privateness settings to your cloud accounts and management who has entry to your recordsdata. Keep away from storing extraordinarily delicate data within the cloud in case you’re involved about safety. Contemplate encrypting recordsdata earlier than importing them.
- Use Safe Communication Channels: When sharing delicate data, use encrypted messaging apps or e mail providers that provide end-to-end encryption. These providers be certain that solely you and the meant recipient can learn the messages.
- Repeatedly Monitor Accounts: Repeatedly overview your on-line accounts for any suspicious exercise, similar to unauthorized logins or modifications to your profile data. Arrange alerts for uncommon exercise. Should you detect any suspicious exercise, change your passwords instantly and speak to the platform’s assist crew.
Reporting Leaked Content material to Related Platforms and Authorities
If non-public media is leaked, swift motion is essential. The method entails figuring out the platforms the place the content material is circulating and reporting the violations to these platforms and probably regulation enforcement.
- Determine the Platforms: Decide the place the leaked content material is being shared. This will embody social media platforms (Fb, Instagram, Twitter, TikTok), video-sharing websites (YouTube, Vimeo), image-hosting websites, and probably even on-line boards or file-sharing web sites.
- Collect Proof: Accumulate as a lot proof as potential, together with screenshots of the leaked content material, URLs of the posts or pages the place it seems, and any figuring out details about the people sharing the content material. This documentation is crucial for reporting the content material and for potential authorized motion.
- Report back to the Platforms: Every platform has its personal reporting mechanism for content material violations. Search for choices similar to “Report,” “Flag,” or “Contact Us.” Present the platform with all of the proof you might have gathered and clearly clarify why the content material violates their phrases of service (e.g., privateness violation, harassment, non-consensual intimate imagery). Observe up in your reviews to make sure they’re addressed.
- Contact Legislation Enforcement: If the leaked content material entails criminal activity, similar to baby sexual abuse materials or threats, or if you’re being harassed or stalked because of the leak, contact regulation enforcement instantly. Present them with all of the proof you might have collected.
- Search Authorized Recommendation: Contemplate consulting with an legal professional specializing in privateness regulation or cyber regulation. They’ll advise you in your authorized choices, similar to sending cease-and-desist letters to people sharing the content material or pursuing authorized motion towards these answerable for the leak.
- Contemplate a Public Relations Technique: In some circumstances, it might be useful to handle the narrative surrounding the leak. This might contain working with a public relations skilled to regulate the data being disseminated and shield your popularity.
- Doc Every part: Hold an in depth document of all of your actions, together with dates, instances, and communications with platforms, regulation enforcement, and authorized professionals. This documentation can be important if you want to take additional motion.
Preventative Measures Guidelines
Implementing preventative measures reduces the probability of personal media leaks. The next guidelines supplies a framework for minimizing threat:
- ☐ Assess Your Digital Footprint: Repeatedly search your title and usernames on-line to see what data is publicly out there. Determine and take away any content material you do not wish to be public.
- ☐ Restrict Sharing of Delicate Content material: Keep away from sharing intimate pictures or movies, particularly if you’re involved about potential misuse. Should you should share such content material, accomplish that solely by safe, encrypted channels with people you belief implicitly.
- ☐ Be Conscious of Your On-line Habits: Suppose earlier than you put up. Contemplate the potential penalties of sharing data or content material on-line. Assume that something you put up might be seen by anybody, together with potential attackers.
- ☐ Assessment and Replace Privateness Settings: Repeatedly overview and replace the privateness settings on all of your social media accounts and different on-line platforms.
- ☐ Use Safe Gadgets and Networks: All the time use safe gadgets and networks. Keep away from utilizing public Wi-Fi networks for delicate actions.
- ☐ Educate Your self About On-line Threats: Keep knowledgeable concerning the newest on-line threats, similar to phishing scams, malware, and social engineering assaults.
- ☐ Defend Your Bodily Gadgets: Hold your gadgets bodily safe. Don’t depart them unattended in public locations. Use machine monitoring options if out there.
- ☐ Observe Protected Relationships: Train warning in your relationships, each on-line and offline. Be cautious of people who stress you to share intimate content material.
- ☐ Repeatedly Again Up Information: Again up all essential knowledge in your gadgets recurrently. This consists of pictures, movies, and different non-public media.
- ☐ Create a Plan: Have a plan in place in case of a leak. Know who to contact, what steps to take, and how one can handle the scenario.
Final Recap
In conclusion, the ‘finest phia liz leaked’ state of affairs serves as a potent catalyst for a vital dialog. It underscores the pressing want for a collective dedication to digital duty, privateness safety, and a extra empathetic understanding of the human value related to these incidents. From the authorized ramifications to the psychological scars, the journey by this digital minefield calls for vigilance, proactive measures, and a unwavering dedication to safeguarding particular person dignity.
By understanding the complexities and the impression of the discharge of personal media, we will try for a safer and moral digital surroundings. The long run hinges on our capability to be taught, adapt, and construct a world the place privateness is valued and revered, guaranteeing that the digital realm doesn’t turn out to be a device for inflicting lasting hurt.
Useful Solutions
What authorized avenues can be found to somebody whose non-public media has been leaked?
Victims can pursue authorized motion, together with submitting civil lawsuits for defamation, invasion of privateness, and intentional infliction of emotional misery. Prison fees may be pursued towards those that distributed the content material with out consent, relying on native legal guidelines.
How can I take away leaked content material from the web?
You’ll be able to report the content material to the platform the place it is hosted, request removing by authorized channels, and contemplate using content material removing providers. Constructing a powerful search engine marketing () technique to bury the content material may be thought-about.
What steps ought to I take instantly after discovering that my non-public media has been leaked?
Doc every thing (screenshots, URLs, and so on.), report the leak to the related platforms, and contemplate looking for authorized and psychological assist. Concentrate on defending your psychological well being and looking for skilled recommendation.
How can I shield myself from future leaks?
Use robust, distinctive passwords, allow two-factor authentication, be cautious about sharing private data on-line, and overview privateness settings on all social media accounts. Repeatedly overview and replace your safety measures.
How can I assist somebody who’s a sufferer of a media leak?
Supply emotional assist, pay attention with out judgment, and encourage them to hunt skilled assist. Respect their privateness, and keep away from sharing or re-posting the leaked content material. Present sources for authorized and psychological help.